The Reply Allpocalypse is something everyone who has ever been on a large email list (NYU, Columbia). It’s an amateur mistake but it starts out with someone send an email to the entire list but is then compounded when people on the list (the larger the initial list, the more chances they’ll be some jokers in there that don’t understand how email works) start to reply and, instead of replying to the sender, decided that everyone on the list needs to see their response.
As the thread continues, everyone’s inbox starts to fill up with further replies of things like “unsubscribe” or “stop spamming me!!” that are also sent to the entire list. This can spiral out of control and bring a mail server to it’s knees and totally take out any mobile mail clients that are frantically trying to keep up.
At some point, people begin to realize that the list is a way for anyone to push a message to everyone at the entire company so you get and “open mike” situation where everyone who has had anything to stay will jump on the bandwagon with their own one-liner they just had to share.
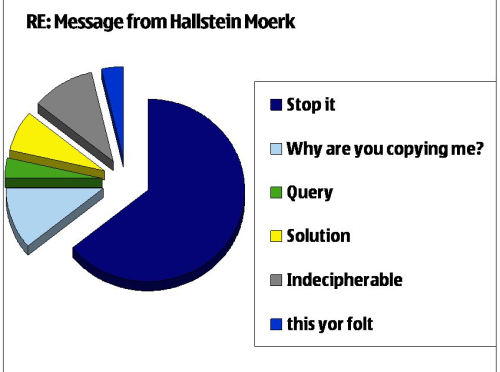
The graphic above is from one such incident that happened while I was at Nokia. I don’t even remember the initial email but it was sent to a large list, could have been the entire company which I think is over 100k souls. As the Reply Alls started to pile on, everyone’s inbox was momentarily taken over and then someone helpfully decided to make an infographic of the type of responses that piled up.
Most famously was the “this yor folt” which came from someone in one of the Central European offices. English was obviously not his first language but his one-liner kicked off a whole new thread of people who started a new thread to poke fun at his butchering of the language as a representation of the folks who kept hitting Reply All to vent and complain, not realizing that they were actually compounding the problem.
If you’re going to send out a mass email, the BCC is your friend.